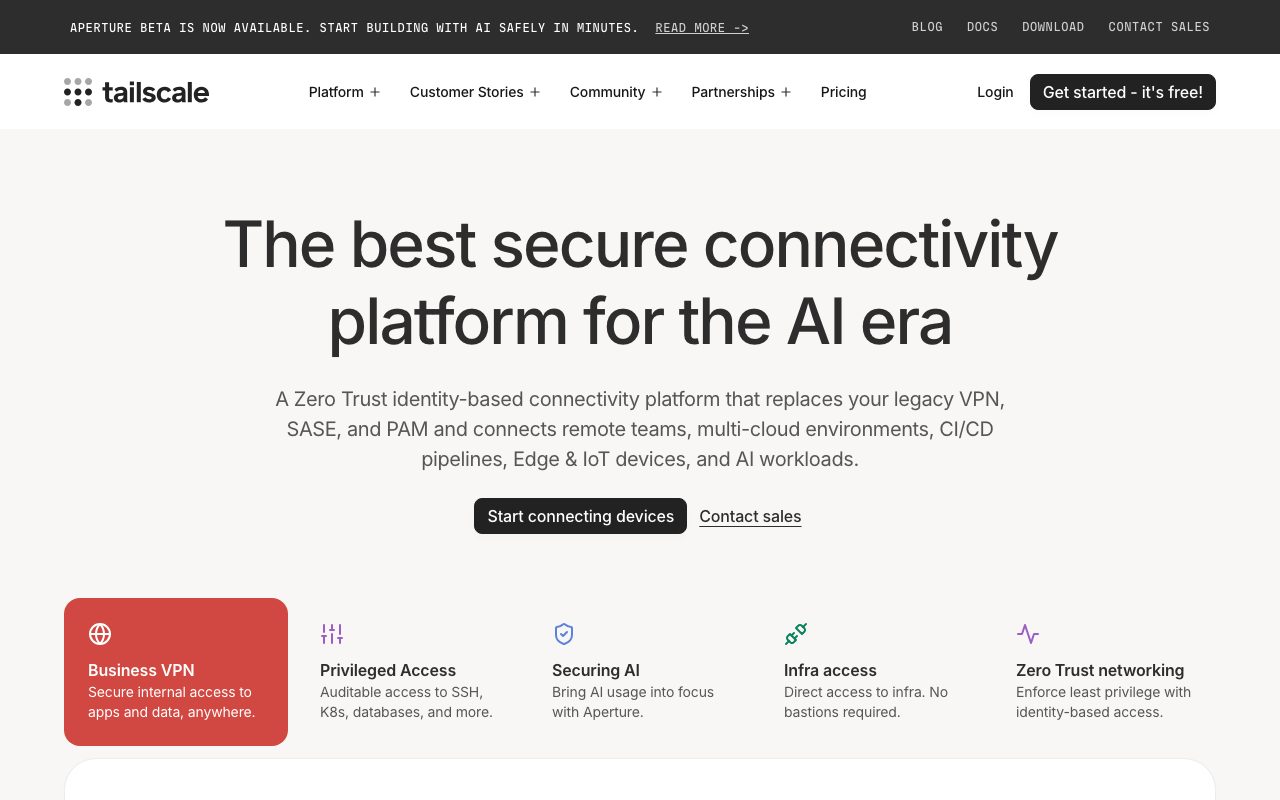
Tailscale
WireGuard-based mesh VPN that connects your devices, servers, and cloud resources into one private network in minutes.
Gallery
About Tailscale
Tailscale is the WireGuard-based mesh VPN that makes connecting your devices, servers, and cloud resources feel embarrassingly easy. Install the client, log in with Google or GitHub, and your machines join a private network in minutes. Compared to legacy corporate VPNs, the experience is borderline magic.
Engineers who've fought OpenVPN, IPsec tunnels, or per-device certificate management tend to react to Tailscale with disbelief. It just works. The mesh topology, automatic NAT traversal, and identity-based ACLs solve problems IT teams used to spend quarters on.
For development teams, home labs, distributed startups, and any company tired of legacy VPN pain, Tailscale is one of the most opinion-changing tools in the infra category.
What Tailscale actually does
Tailscale builds a WireGuard mesh between your devices. Every machine talks directly to every other machine over encrypted tunnels. There's no central VPN server choking the traffic; the topology is genuinely peer-to-peer.
Identity-based access lives in HuJSON ACL files. Define who can talk to what based on user identity, group membership, or device tags. Changes apply in seconds across the entire network.
Subnet routers extend Tailscale into existing network segments. One Tailscale node bridges a home network or AWS VPC, no client install required on every box. Exit nodes route all traffic through a chosen device for full-tunnel use cases.
Tailscale SSH replaces SSH key management with short-lived certificates issued through identity. No more "lost the key" or "rotate everything" emergencies.
Who Tailscale is for
Distributed engineering teams replacing legacy corporate VPNs. The onboarding speed alone (minutes vs days) saves IT real time, every new hire.
Home lab enthusiasts connecting laptops, servers, and Raspberry Pis across networks. The free Personal tier is generous enough that hobbyists rarely outgrow it.
Startups linking Kubernetes clusters across cloud regions. Tailscale's subnet routers make multi-cloud, multi-region private networking feel manageable instead of nightmarish.
Anyone securing access to internal admin dashboards, staging environments, or databases. ACLs make "only Bob from the platform team can hit the staging Postgres" trivial to enforce.
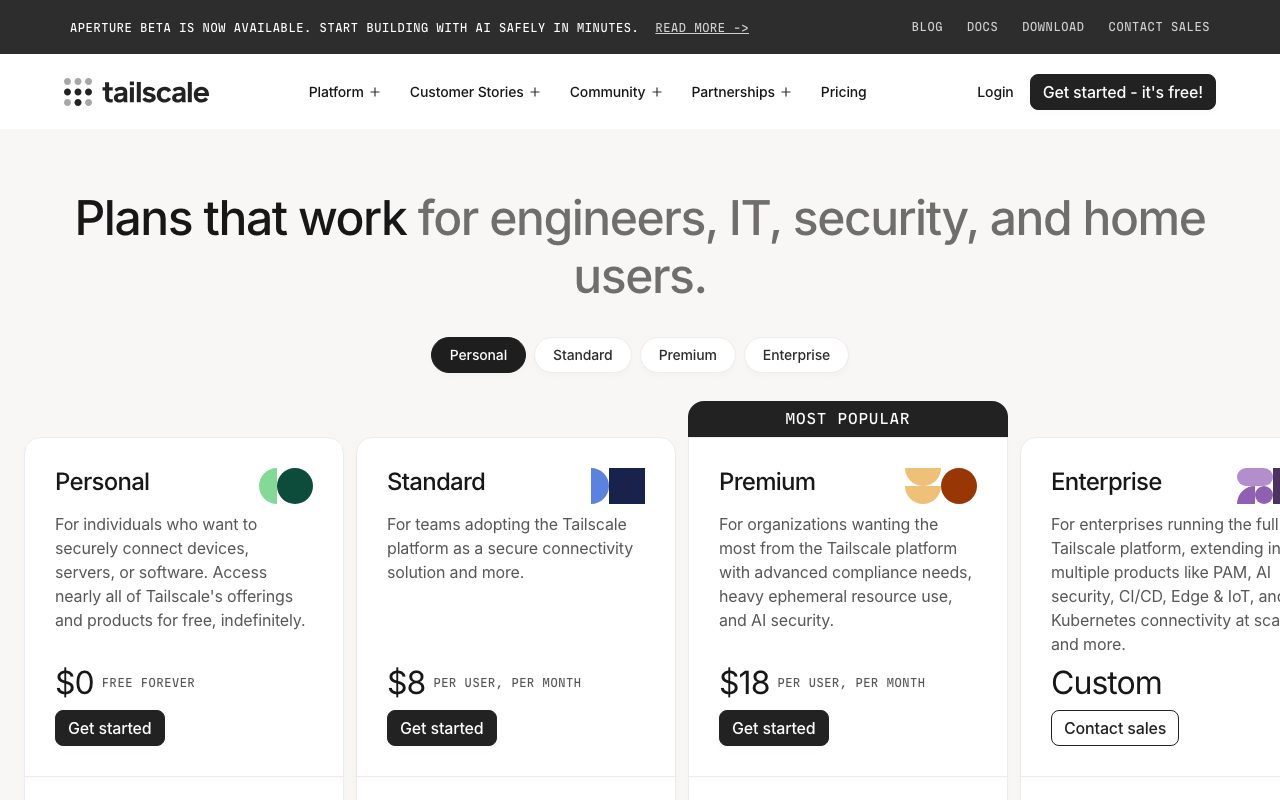
Pricing breakdown
Tailscale's free Personal tier covers up to 100 devices and 3 users. It's not a toy; many indie developers and homelabbers use it indefinitely.
Starter at $6 per user per month adds organizational features. Premium at $18 per user per month adds advanced ACLs, audit logs, and conditional access.
Enterprise tiers include SLA support, advanced compliance, and on-premise control planes. Compared to enterprise VPN licensing, Tailscale's pricing is dramatically friendlier.
Standout features in Tailscale
Onboarding is genuinely measured in minutes. Install client, log in, you're on the network. New hire onboarding flows benefit enormously from this.
WireGuard performance is excellent. Tailscale doesn't add measurable latency on most paths. Throughput typically saturates the underlying network link.
MagicDNS gives every machine a friendly hostname. SSH to "laptop-tony" without remembering an IP. Small thing, big quality-of-life win.
Tailscale SSH
Identity-based SSH with short-lived certificates eliminates SSH key sprawl. Combine with ACLs and you've replaced a dozen SSH-key management workflows with one identity-aware system.
Honest tradeoffs
The coordination server is hosted by Tailscale by default. Purists who want full self-hosting run Headscale, the open-source coordination server. Most teams happily use the hosted version.
Power-user features (advanced ACLs, audit logs, SSO via SAML) sit in higher tiers. Free Personal works great for solo use; teams hit upgrade triggers fairly quickly.
Latency on heavily NAT'd paths can be slightly worse than direct connections. Tailscale's DERP relays handle the worst cases, but P2P is the happy path.
Tailscale is one of those rare tools where the marketing claims undersell the actual experience. Engineers who try it generally don't go back.
Tailscale vs alternatives
Versus traditional VPNs (OpenVPN, IPsec, AnyConnect), Tailscale wins on every dimension that matters in 2026: setup time, performance, maintenance, identity integration. The legacy tools survive on enterprise inertia.
Versus ZeroTier, Tailscale wins on UX polish and identity integration. ZeroTier wins on flexibility for complex network topologies. See the comparison.
Versus Cloudflare Tunnel and Tailscale's own offering, both target similar use cases for inbound connectivity. Tailscale's mesh model is more flexible for bidirectional traffic.
For more options, see the best mesh VPNs and Tailscale alternatives.
Bottom line
Tailscale is the right call for nearly any team that wants private networking without legacy VPN pain. The free tier covers individuals and small teams indefinitely; the paid tiers earn their keep at organizational scale.
If you've been putting off "fixing the VPN," try Tailscale on a Saturday. The Sunday version of you will be running it on every machine you own. That's not hyperbole; it's the most common Tailscale adoption story.
Setting up Tailscale right
Sign up with Google, GitHub, or Microsoft identity. SSO from the start beats migrating identity later.
Install the client on every device that should join the network. Each device authenticates against your identity provider and joins the tailnet automatically.
Define ACLs early. The default "everyone can access everything" policy is fine for a personal tailnet and disastrous for a company. Move to explicit allow-lists before you have many users.
ACL patterns that scale
Tag devices by role: "tag:server", "tag:laptop", "tag:db". Tag users by team: "group:platform", "group:product". Write ACLs in terms of tags and groups, not individual identities.
Test ACL changes in staging tailnets before production. Tailscale's ACL syntax is small but unforgiving; a typo can lock people out.
Audit ACLs quarterly. Permissions drift; access creeps; quarterly reviews catch the worst of it before it matters.
Tailscale for k8s and cloud
Tailscale's k8s operator deploys subnet routers and proxies inside clusters. Pod-to-pod connectivity across clusters becomes trivial.
Cloud subnet routers bridge AWS, GCP, and Azure VPCs into the tailnet. Multi-cloud private networking that used to require dedicated network engineering is now an afternoon project.
Tailscale Funnel exposes specific services to the public internet over Tailscale's network. Useful for demos, webhooks, and one-off public endpoints without provisioning real load balancers.
Common Tailscale questions
Is Tailscale really free for personal use? Yes, up to 100 devices and 3 users. Most individuals never hit the limits.
Can Tailscale replace a corporate VPN entirely? For most modern companies, yes. Legacy enterprises with specific compliance constraints may need to evaluate carefully.
Does Tailscale work with site-to-site VPN setups? Yes. Subnet routers handle the bridging without major reengineering.
Browse more at tools for network security.
Tailscale for home labs
Tailscale is the obvious choice for connecting home servers, NAS boxes, and remote management. The free tier easily covers most home lab setups.
Subnet routers let you reach an entire home network from anywhere. Plex, home automation, file shares, all accessible without VPN reconfiguration.
The mobile app gives you tailnet access from phones cleanly. Useful for SSH'ing to home boxes during travel or emergencies.
Tailscale for developer teams
Engineers connect to staging databases, internal admin dashboards, and Kubernetes clusters through Tailscale instead of bastion hosts. The DX improvement is meaningful.
SSH key management essentially disappears with Tailscale SSH. Identity-based access plus short-lived certificates replace the keys-and-bastions model.
Tag-based ACLs scale well as the team grows. Developers, ops, contractors all get appropriately scoped access without bespoke firewall rules per role.
Headscale for self-hosters
Headscale is the open-source coordination server. Run your own control plane if you need to. Most teams happily use Tailscale's hosted plane; the option matters for the few that don't.
Final thoughts on Tailscale
Tailscale is one of the rare tools that genuinely changes how engineers think about a problem. Connecting devices used to be a project. With Tailscale, it's a checkbox.
The pricing scales reasonably. The free tier is generous for individuals. The paid tiers earn their keep at organizational scale. There's no version of this product that feels like a rip-off.
Browse other options at the best VPN tools and remote access tools.
Quick recap
Tailscale fits distributed engineering teams, home labs, multi-cloud deployments, and anyone tired of legacy VPN pain. The onboarding speed and identity-aware ACLs are the standout features.
The free tier is generous enough that most individuals never upgrade. Paid tiers earn their keep at organizational scale.
Pair it with Tailscale SSH for identity-based server access. The combination replaces SSH key management with something genuinely better.
Browse more options at the best network tools, the DevOps tools category, and Tailscale alternatives.
Tailscale closing notes
Few tools change "how do we do this?" answers as quickly as Tailscale does. Networking problems that used to take weeks dissolve into afternoons.
The community around Tailscale is genuinely useful. Forums, GitHub discussions, Reddit threads. Solutions to almost any setup question are findable within minutes.
For organizations migrating from legacy VPNs, plan a parallel-run period. Run Tailscale alongside the old VPN for a month before flipping the switch. The transition is smoother and the rollback path is preserved.
Browse more network options at the best zero-trust tools and the broader private networking category.
Tutorial / Demo
Key Features
- WireGuard mesh with automatic NAT traversal
- Identity-aware ACLs in HuJSON
- Subnet routers and full-tunnel exit nodes
- Tailscale SSH with short-lived certificates
- MagicDNS for human-friendly hostnames
Pros & Cons
What we like
- Onboarding is genuinely a few minutes, not a few days
- Free Personal tier is more than a toy
- WireGuard performance and security model are excellent
Room for improvement
- Coordination server is hosted, so purists self-host Headscale instead
Frequently Asked Questions
Is Tailscale free for personal use?
Tailscale vs WireGuard, what's the difference?
Can I self-host Tailscale's control plane?
Does Tailscale work on mobile?
Are there any privacy concerns with Tailscale?
Best For
Featured in
Tags
Alternatives to Tailscale
View allTurborepo
High-performance build system for JavaScript and TypeScript monorepos

Loops
Modern email platform built for SaaS teams, combining transactional, marketing, and lifecycle messages with a clean API.

Lucide
Open-source icon library, a community-led fork of Feather, with 1,500+ consistent icons and bindings for every major framework.
Heroicons
Free, MIT-licensed SVG icon set crafted by the Tailwind Labs team, with outline, solid, mini, and micro variants.
Reviews (10)
Worth the price of admission
Six months of using Tailscale, here's what holds up. Honestly impressed by how wireGuard performance and security model are excellent. The tailscale SSH with short-lived certificates is more useful than I expected.
Honest take after six months
Been using Tailscale for six months now. Where it really wins is onboarding is genuinely a few minutes, not a few days. Got real value out of subnet routers and full-tunnel exit nodes. Main use case: securing access to internal admin dashboards.
Pros
- WireGuard performance and security model are excellent
Solid daily driver
Tailscale has quietly become part of my daily flow. What stands out is how free Personal tier is more than a toy. Their take on subnet routers and full-tunnel exit nodes is solid. It fits well for securing access to internal admin dashboards. Easy yes for anyone weighing the same trade-offs.
Pros
- WireGuard performance and security model are excellent
Maybe in a year when they fix the basics
Tailscale solves a real problem for me, but it's not magic. Genuine strength: free Personal tier is more than a toy. It would be a 5 if not for coordination server is hosted — purists self-host Headscale instead.
Pros
- Onboarding is genuinely a few minutes, not a few days
- Free Personal tier is more than a toy
Cons
- Coordination server is hosted — purists self-host Headscale instead
Does the job, doesn't sparkle
Hadn't planned on switching, but Tailscale was hard to ignore. The thing I keep coming back to: free Personal tier is more than a toy. Main use case: linking k8s clusters across cloud regions. Not perfect but better than the alternatives I tried.
Cons
- Coordination server is hosted — purists self-host Headscale instead
Tailscale, better than expected
Been using Tailscale for the past year now. The thing I keep coming back to: wireGuard performance and security model are excellent. That said, coordination server is hosted — purists self-host Headscale instead is a real gripe. Hard to imagine going back to my previous setup.
Cons
- Coordination server is hosted — purists self-host Headscale instead
Pulled its weight from week one
Honest take: Tailscale delivers most of what the marketing promises. What stands out is how wireGuard performance and security model are excellent. Found it works best for connecting laptops to home servers and home labs.
Pros
- Free Personal tier is more than a toy
Underrated honestly
Tailscale isn't perfect but it's the best I've used in this category. Genuine strength: onboarding is genuinely a few minutes, not a few days. The identity-aware ACLs in HuJSON is more useful than I expected. Still recommending it to people in similar setups.
Pros
- Onboarding is genuinely a few minutes, not a few days
- WireGuard performance and security model are excellent
- Free Personal tier is more than a toy
Genuinely impressed
Took a few weeks for Tailscale to click, then it stuck. What stands out is how onboarding is genuinely a few minutes, not a few days. Worth calling out the identity-aware ACLs in HuJSON too. Would buy again without thinking twice.
Pros
- Free Personal tier is more than a toy
- WireGuard performance and security model are excellent
The kind of tool you forget you're paying for
Got Tailscale on the recommendation of someone I trust. What stands out is how wireGuard performance and security model are excellent. Magicdns for human-friendly hostnames works the way you'd hope. It fits well for securing access to internal admin dashboards.
Pros
- Free Personal tier is more than a toy
- Onboarding is genuinely a few minutes, not a few days
- WireGuard performance and security model are excellent